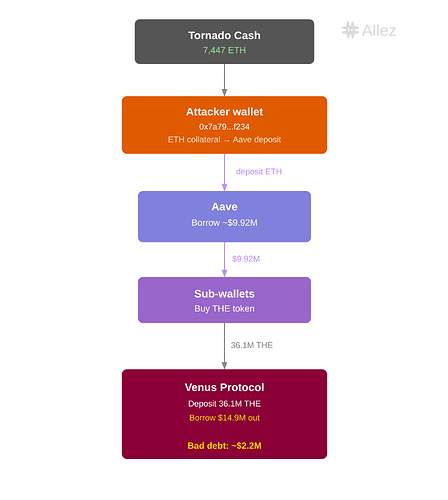
On March 15, 2026, an attacker executed an attack against the THE (Thena) market on Venus Protocol (BNB Chain). The attack exploited compounding weaknesses: thin liquidity for THE, and a “donation” mechanic in Venus’s Compound-forked architecture that allowed the attacker to bypass the market’s supply cap.
The attacker deposited 53.2 million THE as collateral - 3.67x the 14.5M supply cap - and borrowed approximately $14.9M in assets (CAKE, BNB, WBNB, USDC, BTCB) against the inflated position. The subsequent unwinding and liquidation cascade left Venus with just over ~$2M in bad debt.
Incident Timeline
All timestamps are UTC. Block references are on BNB Chain.
| Roles | Address |
|---|---|
| Original supplier - the primary attacker address | 0x1a35bd28efd46cfc46c2136f878777d69ae16231 |
| Attacker contract | 0x737bc98f1d34e19539c074b8ad1169d5d45da619 |
Phase 1 - Preparation (June 2025-March 2026)
The attacker began accumulating a large THE position on Venus over a period of approximately nine months. By March 15, the primary attacker address (0x1a35) held approximately 12.2M vTHE (84% of the 14.5M supply cap) a position that was technically within protocol limits.
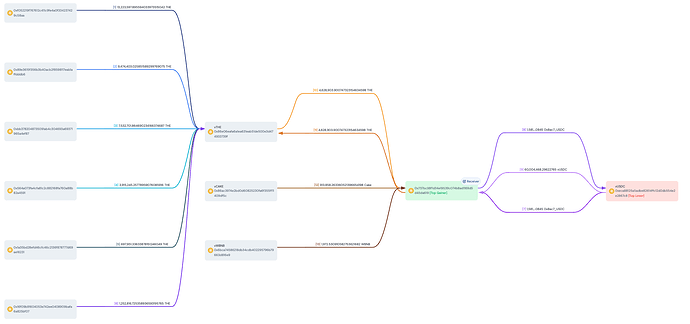
A wallet (0x7a79…f234) received 7,447 ETH (~$16.29M) in 77 transactions from Tornado Cash between 9 and 1 months ago (typical tx). The attacker deposited this ETH as collateral on Aave (typical tx), borrowing approximately $9.92M in stablecoins (USDT, DAI, USDC). These funds were dispersed to intermediary addresses to purchase additional THE.
Phase 2 - Initial Attack (~11:55 UTC)
The attacker initiated the core attack in a single transaction by deploying an attack contract.
Attack transaction: 0x4f477e941c12bbf32a58dc12db7bb0cb4d31d41ff25b2457e6af3c15d7f5663f
Within the constructor of this contract, the following actions were executed atomically:
- Exchange rate manipulation via donation: Six wallets transferred a combined ~36M THE directly to the vTHE contract, inflating the exchange rate. Among these wallets, 0x1a35 was the existing supplier controlling 84.4% of vTHE supply. The attack contract (0x737b) held no collateral itself but was granted permission to use 0x1a35’s borrowing power.
- Initial borrows: The attack contract borrowed 1.58M USDC from Venus and immediately re-supplied it back (likely a test of the exploit path). It then borrowed 4.6M THE and transferred it directly to the vTHE market - further inflating the exchange rate.
- Asset extraction: The attack contract borrowed 910K CAKE and 1,972 BNB.
The exchange rate was inflated from 10,086,934,836 → 38,420,106,438 (3.81×). The impact on the original supplier (0x1a35) is shown below. In effect, the donation of ~40.7M THE 10×’d the borrowing power of the existing position.
| Before Attack | After Attack | |
|---|---|---|
| Supply | ~12M THE (~$3.30M) | Same vToken amount, now worth ~45M THE (>$12M) |
| Borrow | ~900K CAKE (~$1.28M) | ~900K CAKE (~$1.28M, unchanged) |
| Borrowing power remaining | ~$0.47M | ~$5.08M |
Using the stablecoins borrowed via Aave, the attacker was buying THE, and the price was driven from ~$0.26 to nearly $4 on Binance Oracle. Venus’s Resilient Oracle (RedStone as primary, Binance as pivot) initially rejected the spiking price - the BoundValidator reverted for approximately 37 minutes as the Binance feed diverged wildly. As the attacker sustained buy pressure across multiple venues in RedStone’s aggregation, both feeds eventually converged at the elevated level, BoundValidator accepted the price, and the protocol began valuing THE collateral at the manipulated rate.
Phase 3 - Follow-Up Attacks (~12:00–12:42 UTC)
Following the initial attack, both addresses executed follow-up transactions to amplify the position further:
Original supplier (0x1a35): Repeatedly borrowed 100 BNB → swapped to THE with the recipient set directly to the vTHE contract (typical tx), combining price pumping and exchange rate inflation in a single step.
Attack contract (0x737b): Continued a borrow → swap → donate loop (typical tx), further inflating the exchange rate and pumping THE’s price in the process.
This drove the supply cap breach progressively higher until it’s peak:
| Time (UTC) | THE Supplied | vs. 14.5M Supply Cap |
|---|---|---|
| 11:00 | 12,234,411 | 84% - within limits |
| 12:00 | 49,525,348 | 341% - cap bypassed |
| 12:42 | 53,230,145 | 367% - peak before liquidation |
THE’s price was pushed to ~$0.51 when the attack stopped. At peak (block 86738236, 12:42 UTC), the positions stood at:
Original supplier (0x1a35):
| Side | Asset | Amount (Token) |
|---|---|---|
| Supply (collateral) | THE | 53,230,145 |
| Borrow | CAKE | 6,669,112 |
| Borrow | BNB | 2,801 |
| Borrow | WBNB | 1,972 |
| Borrow | USDC | 1,581,461 |
| Borrow | BTCB | 20 |
Attack contract (0x737b):
| Side | Asset | Amount (Token) |
|---|---|---|
| Supply (collateral) | USDC | 1,581,455 |
| Borrow | THE | 4,628,904 |
Phase 4 - Collapse and Liquidation (~12:42 UTC onward)
The attacker’s health factor was driven close to 1. When selling pressure overwhelmed the thin bid-side liquidity, THE’s price collapsed to ~$0.22 (below the pre-attack level) as both liquidation bots and panicked holders sold into the crash.
Cascading liquidations unwound approximately 42M THE in collateral. While liquidators recovered partial value, the gap between the nominal collateral valuation and realizable market value left the protocol with ~$2.18M in bad debt (primarily denominated in CAKE and THE).
The positions ended at:
Original supplier (0x1a35):
| Side | Asset | Amount (Token) | Amount ($) |
|---|---|---|---|
| Supply (collateral) | THE | 0.6 | $0 |
| Borrow | CAKE | 1,184,089 | $1,792,379 |
Attack contract (0x737b):
| Side | Asset | Amount (Token) | Amount ($) |
|---|---|---|---|
| Supply (collateral) | USDC | 0.16 | $0 |
| Borrow | THE | 1,846,476 | $358,585 |
Root Cause Analysis
The exploit combined three factors:
1. Supply Cap Bypass via Donation Mechanic
Venus’s architecture allows direct token transfers to market contracts (e.g., vTHE). These “donations” increase the contract’s token balance and by extension, the recognized collateral - without passing through the mint pathway where supply caps are enforced.
The vulnerable code path:
In the vToken contract, getCashPrior() reads the underlying token balance directly:
// VBep20.sol — Venus Protocol core pool
// https://github.com/VenusProtocol/venus-protocol/blob/develop/contracts/Tokens/VTokens/VBep20.sol#L245
function getCashPrior() internal view override returns (uint) {
return IERC20(underlying).balanceOf(address(this));
}
This value feeds into the exchange rate calculation where the exchange rate is equal to the total borrowed, minus the total reserves plus the total cash (balanceOf the contract).
// VToken.sol — exchangeRateStoredInternal()
// https://github.com/VenusProtocol/venus-protocol/blob/develop/contracts/Tokens/VTokens/VToken.sol#L1853
function exchangeRateStoredInternal() internal view virtual returns (MathError, uint) {
uint _totalSupply = totalSupply;
if (_totalSupply == 0) {
return (MathError.NO_ERROR, initialExchangeRateMantissa);
} else {
// exchangeRate = (totalCash + totalBorrows - totalReserves) / totalSupply
uint totalCash = _getCashPriorWithFlashLoan();
uint cashPlusBorrowsMinusReserves;
Exp memory exchangeRate;
MathError mathErr;
(mathErr, cashPlusBorrowsMinusReserves) = addThenSubUInt(
totalCash, totalBorrows, totalReserves
);
// ...
(mathErr, exchangeRate) = getExp(cashPlusBorrowsMinusReserves, _totalSupply);
return (MathError.NO_ERROR, exchangeRate.mantissa);
}
}
However, supply caps are only enforced in the mintAllowed function - the Comptroller’s gateway for normal deposits:
// PolicyFacet.sol — mintAllowed()
// https://github.com/VenusProtocol/venus-protocol/blob/develop/contracts/Comptroller/Diamond/facets/PolicyFacet.sol#L33
function mintAllowed(address vToken, address minter, uint256 mintAmount) external returns (uint256) {
// ...
uint256 supplyCap = supplyCaps[vToken];
require(supplyCap != 0, "market supply cap is 0");
uint256 vTokenSupply = VToken(vToken).totalSupply();
Exp memory exchangeRate = Exp({ mantissa: VToken(vToken).exchangeRateStored() });
uint256 nextTotalSupply = mul_ScalarTruncateAddUInt(exchangeRate, vTokenSupply, mintAmount);
require(nextTotalSupply <= supplyCap, "market supply cap reached");
// ...
}
The gap: When THE is transferred directly to the vTHE contract (bypassing mint), getCashPrior() reflects the higher balance, inflating the exchangeRate. But mintAllowed() is never called, so the supply cap is never checked. After the donation of ~36M THE, the exchange rate inflated 3.81× (from 10,086,934,836 to 38,420,106,438), meaning the same vToken holdings were now worth dramatically more, enabling the attacker to borrow far beyond what the supply cap was designed to allow.
This vector was identified in a prior Code4rena audit (2023-05-venus) but was assessed as having “no negative side effects” and was not remediated.
2. Illiquid Collateral + Price Manipulation
THE’s Resilient oracle (RedStone as primary, Binance as pivot) reflected aggregated prices. During the manipulation window, the BoundValidator repeatedly rejected the price, the ResilientOracle reverted for ~37 minutes while Binance spiked wildly. Both feeds eventually converged at the elevated level when the BoundValidator accepted it as valid.
3. Concentration Risk in Isolated Markets
The attacker was able to accumulate ~84% of the supply cap over nine months. In a low-liquidity market it is not infrequent, but this level of concentration can offer preconditions for manipulation.
Impact Assessment
Financial
- Bad debt: ~$2.15M (1.18M CAKE + 1.84M THE equivalent, unpaid). To be covered by the protocol.
- THE price impact: ~$0.26 → nearly $4 on Binance oracle, ~$0.51 redstone resilient oracle → ~$0.22 (post-liquidation), representing a ~15% intraday decline from pre-attack levels
Operational
- Limited to the THE and CAKE markets
- In an abundance of caution BCH, LTC, UNI, AAVE, POL, FIL, TWT, lisUSD markets have had their CF set to 0.
Attacker Profit
On-chain analysis indicates the attack was unprofitable on-chain - the attacker’s collateral was liquidated at depressed prices, and traceable wallet flows show no net gain. The strategy could include independent wallets or CEX accounts, to long/short THE. We are coordinating with exchanges and forensic partners to pursue this line of investigation.
Remediation
Immediate (Completed)
- Paused borrowing and withdrawals in affected markets
- Set CF = 0 in potentially at risk markets as a precautionary measure
- Attacker addresses flagged and shared with forensic partners
- Concentration monitoring: Automated flagging of wallets approaching significant fractions of supply caps
Short-Term (In Progress)
- Donation mechanic hardening: Enforce supply cap checks on all balance increases to the market contract, not only the
mintpathway - Collateral factor and parameter audit: Reduce collateral factors for illiquid assets; introduce more conservative liquidity-weighted calibrations. All market configurations and collateral parameters, with potential delistings
- Governance proposal (VIP) for bad debt resolution
- Coordination with law enforcement on Tornado Cash-sourced funding, and CEX KYD’d activity
Mid-Term (Planned)
- A complete re-audit for the whole core pool
Key Takeaways
Nominal collateral value ≠ realizable liquidation value. When collateral has no real liquidity, the protocol may recognize $30M market capitalisation on paper while the market can only absorb a fraction. This fundamental mismatch is the economic vulnerability that oracle manipulation attacks exploit.
Audit findings require follow-through. The donation bypass was flagged but dismissed. In adversarial environments, any mechanism that circumvents a safety parameter must be treated as a potential attack vector, regardless of whether an immediate exploit path is apparent at audit time.
Illiquid collateral demands proportionally stricter parameters. Supply caps, collateral factors, and oracle configurations must be aligned to latest realizable market depth.
Conclusion
The March 15 THE market manipulation was a sophisticated, premeditated attack that exploited a known architectural gap in supply cap enforcement. The ~$2M in bad debt is being addressed through governance.
We are continuing our investigation alongside Venus and security partners.
All updates will be shared through official @VenusProtocol channels and @AllezLabs.